WE ARE
The NorthCap University
Best Private University in Delhi / NCR
Delivering excellence in education since 1996
- The NorthCap University (NCU) is a progressive multidisciplinary top university located in the city centre of Gurugram, Haryana. The university’s rich heritage of 25+ years, 11000+ alumni and robust academic infrastructure enables deep linkages with government, industry and research bodies. The university operates three schools in its state-of-the-art urban campus and hosts a diverse student body in the disciplines of engineering & technology, management, liberal arts, law, and applied sciences.
- NCU is a National Assessment and Accreditation Council (NAAC) Grade A accredited university that serves as a research and talent catalyst between students and industry. Guided by eminent academicians and industry leaders, it follows an immersive pedagogy to deliver undergraduate, postgraduate and doctoral programmes. The university is a comprehensive partner of Arizona State University (#1 university in the U.S. for innovation, outreach and stewardship). This strategic collaboration focuses on innovation, internationalisation and digitisation. NCU students enjoy summer immersion programme and accelerated master’s programmes in the US given this partnership.
- NCU is recognised by the University Grants Commission (UGC) and the Bar Council of India (BCI). It is a member of the Association of Indian Universities (AIU), member of the Association of Commonwealth Universities (ACU) UK, a member of the American Society for Quality and is accredited by Accreditation Services for International Colleges (ASIC), UK. With a 5-Star QS Ranking for Teaching, Employability, Academic Development, Online Learning and Inclusiveness, NCU ranks among the 30 Best Performing Top Universities for Engineering in India as per Atal Ranking of Institutions on Innovation Achievements (ARIIA) rankings.

Our Schools
Why
NCU, GURUGRAM?
Alliances and Collaborations










Webinars

Ms Shikha Yadav & Ms. Jiveta chaudhary
Faculty, SOM & LS

Dr. Akshat Rao & Dr. Kanchan Yadav
Faculty, SOM &LS
Mr. Ashish Budhwar & Ms. Saniya Bhutani
Psychology faculty from School of Management and Liberal Studies

Mr. Salman Waris
LLM from the University of Essex

Dr. Nishi Gupta
(Faculty, SOET)
Dr. Sona Vikas
Professor & Head-SOM&LS
Dr Ashima Saxena and Dr Akasha Sandhu
Faculty of SOM&LS
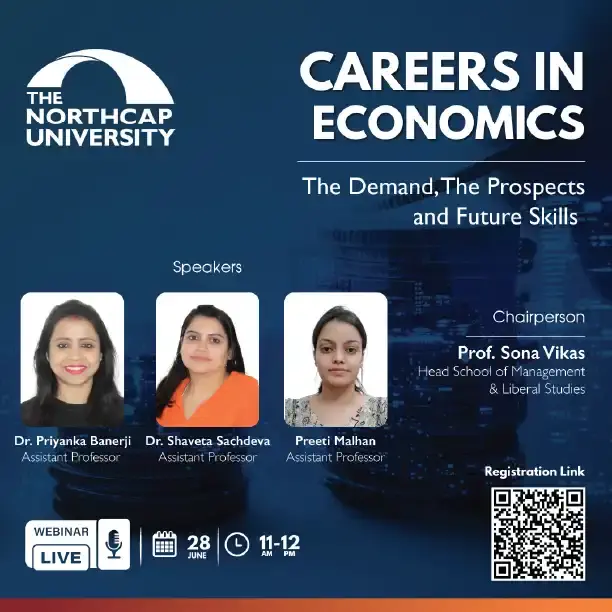
Dr Priyanka Banerji, Dr Shaveta Sachdev and Ms Preeti Malhan
(Faculty of SOM&LS)
Our Prestigious Recruiters
Master Class

Pratibha Maninder Singh
Justice in the Delhi High Court

Gyan Sudha Misra
Chief Justice of the Jharkhand High Court
Saurabh Kripal
Senior Advocate at the Supreme Court of India

Meghna Mishra
Prominent lawyer and partner at Karanjawala & Co

Gaurav Sarup
Director - ESG, Carbon & Social Performance at Vedanta Resources Limited

Apurva Chamaria
Head of Startups and Venture Capital as well as Partnership Solutions at Google India

Rashi Narang
Founder of Heads Up For Tails

Vidya Bhushan
The COO and Co-Founder of Daalchini Technologies

Mr. Rajit Sikka
Regional Head, Academic interface program-North TCS

Mr. Varinder Singh
Chief Manager-HR, Fortum India

Shree Parthasarathy
Managing Partner - Consulting, Technology and Transformation

Dr. Emiliano Diez
Head - Product Development and Client Services - Cintana Education

Chandresh Daftary
Regional Director (Operations) - PVR Cinemas

Vinay Solanki
Head Digital Solutions - Napino Auto & Electronics Ltd.

Prof. Milind Padalkar
Operations and Systems at Bennett University School of Management

Gita Mittal
Hon'ble Chief Justice (Retd.) - High Court of Jammu & Kashmir and Ladakh

Neel Broker
President, Asia-Pacific - Cintana Education

Shoma Chaudhury
Journalist - Editor & Political Commentator

Nitin Pai
Co-founder and Director - Takshashila Institution

Venkatesh Sarvasiddhi
Managing Director (MD) of Springer Nature India

Jayaseelan Ganesan
Entrepreneurial Champion

A virtual masterclass on
Designing My Learning Journey Leveraging Design Thinking Principles
read moreDr. Anbu Rathinavel
Ph.D. Artificial Intelligence Chief Mentor - Life Design Lab

A virtual masterclass on
Life skills for success foundations of excellence in all aspects of life
read moreSanjay Sahay
Principal Consultant - Creation of Future

Pradeep Shrivastava
Chief Commercial Officer, Axiata Digital.
Lt Gen I S Singha AVSM, VSM (Retd) Director
Global and Government Affairs - TAC Security

Dr. Saumen Chakraborty
Advisor of Dr. Reddy’s Laboratories

Maj Gen Vikram Dev Dogra
AVSM - Commanding 17 Poona Horse Motivational & Leadership Speaker, Army General

Sanjeev Bikhchandani
Co-founder - Info Edge

A virtual masterclass on
Importance Of Accreditations Why Study At An Accredited Institution?
read moreDr. Agueda Benito
Chief Academic Officer - Cintana Education
A virtual masterclass on
Challenges and Opportunities For India's Economy In The Post-Covid Era
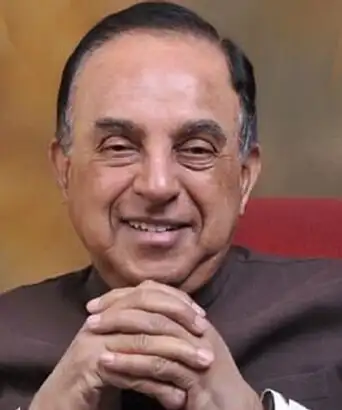
read moreDr. Subramanian Swamy
Member of Parliament - Rajya Sabha

Dr. R. F. "Rick" Shangraw Jr.
President - Cintana Education

Dr. Rakesh Godhwani
Founder of the School of Meaningful Experiences and an Adjunct Faculty at IIMB
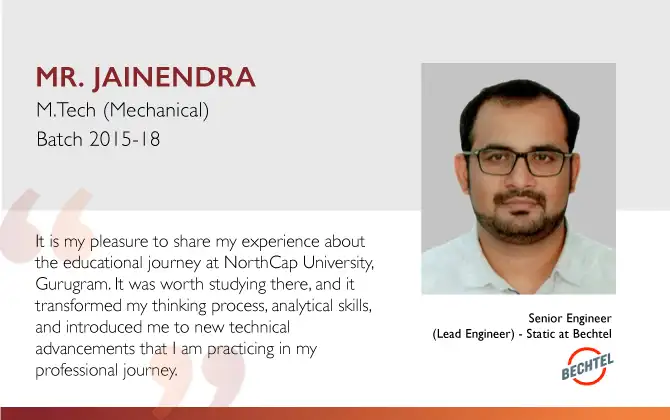
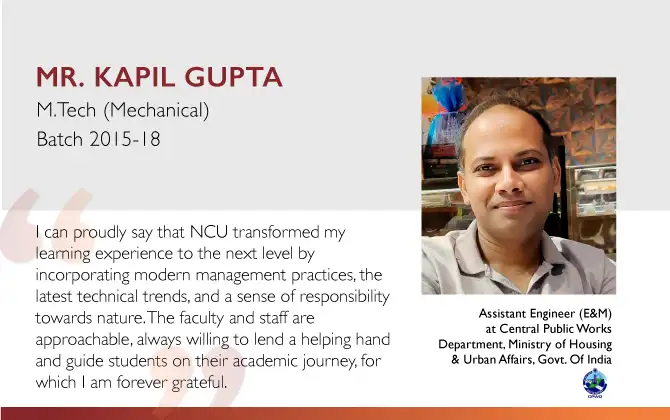
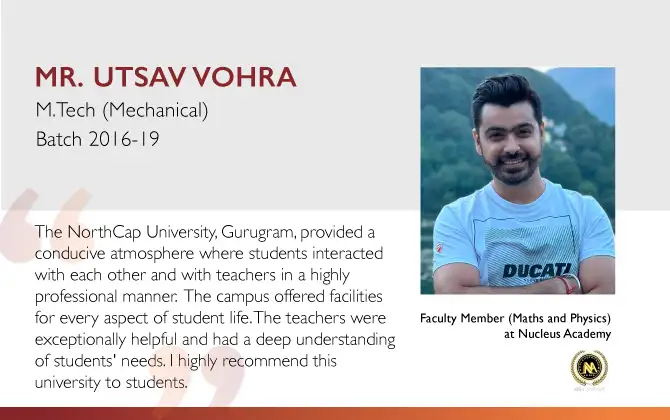
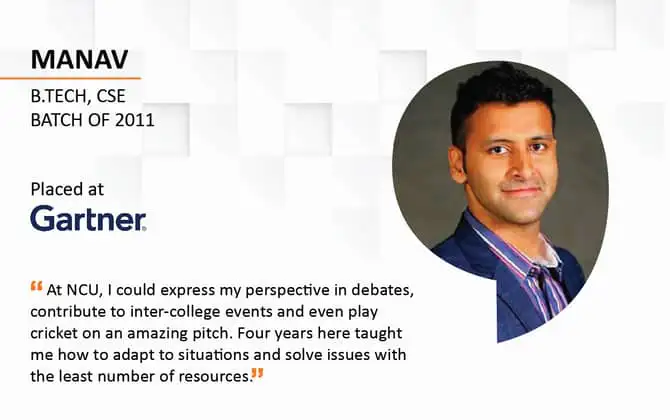
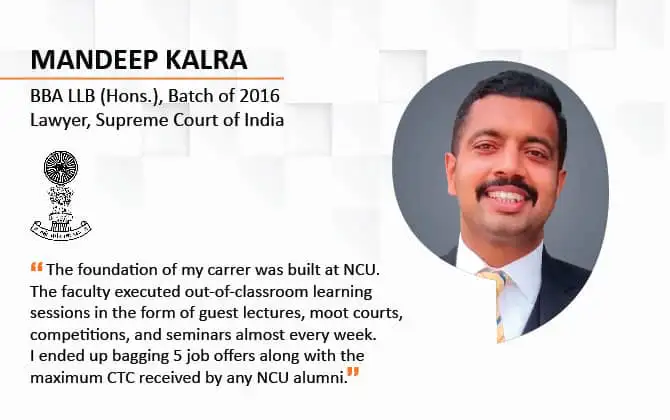
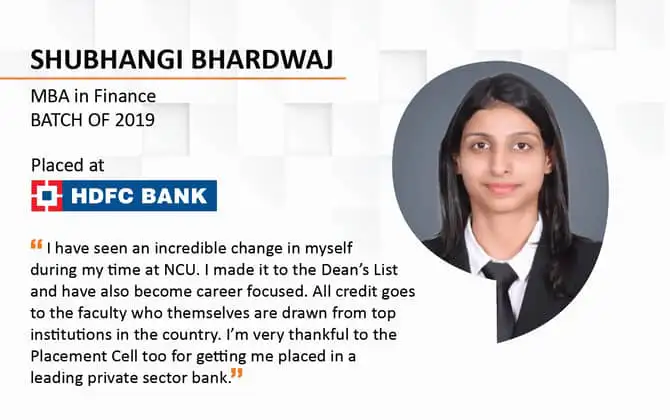
Success Stories